Back in the day if you wanted your servers to live a happy stress free life you sent them to a colo, a boarding school for servers in a sense. In return they got their own secure floor space, perfect HVAC and power, along with lots of bandwidth. The only problem was that everything was physical including your routers and firewalls, which means they require extra power and rack space, and in a colo type environment rack space and power both cost money!
New technologies like VMware NSX, Cisco ACI, and other software defined networking technologies are changing things, but most cost a decent amount of money to implement. For my colo, and my budget, I have taken a little bit different approach to securing different portions of my cloud. Open source virtualized firewalls!
 pfSense is a freeBSD based firewall / router that can run as a virtual machine just like anything else, and it works beautifully for controlling traffic in and out of portgroups (tenants) in my cloud. Best of all the price is right! (Free) Sure it isn’t a distributed kernel level router or firewall capable of 10’s of Gbps… but in many cases it will still far exceed my requirements.
pfSense is a freeBSD based firewall / router that can run as a virtual machine just like anything else, and it works beautifully for controlling traffic in and out of portgroups (tenants) in my cloud. Best of all the price is right! (Free) Sure it isn’t a distributed kernel level router or firewall capable of 10’s of Gbps… but in many cases it will still far exceed my requirements.
So inside of my colo “cloud” space I have lots of VLAN’s, some of those VLAN’s are mine and some are for other people. For example, a couple of my friends have some VM’s that they run in my cloud for offsite backup or because their home connection doesn’t work for what they need. So instead of terminating their VLAN at my Cisco ASA firewall I instead terminate it into a pfSense firewall which has a public IP on the outside. This allows them to establish VPN’s to their VLAN as well as create their own NAT and firewall rules all without affecting anyone else.
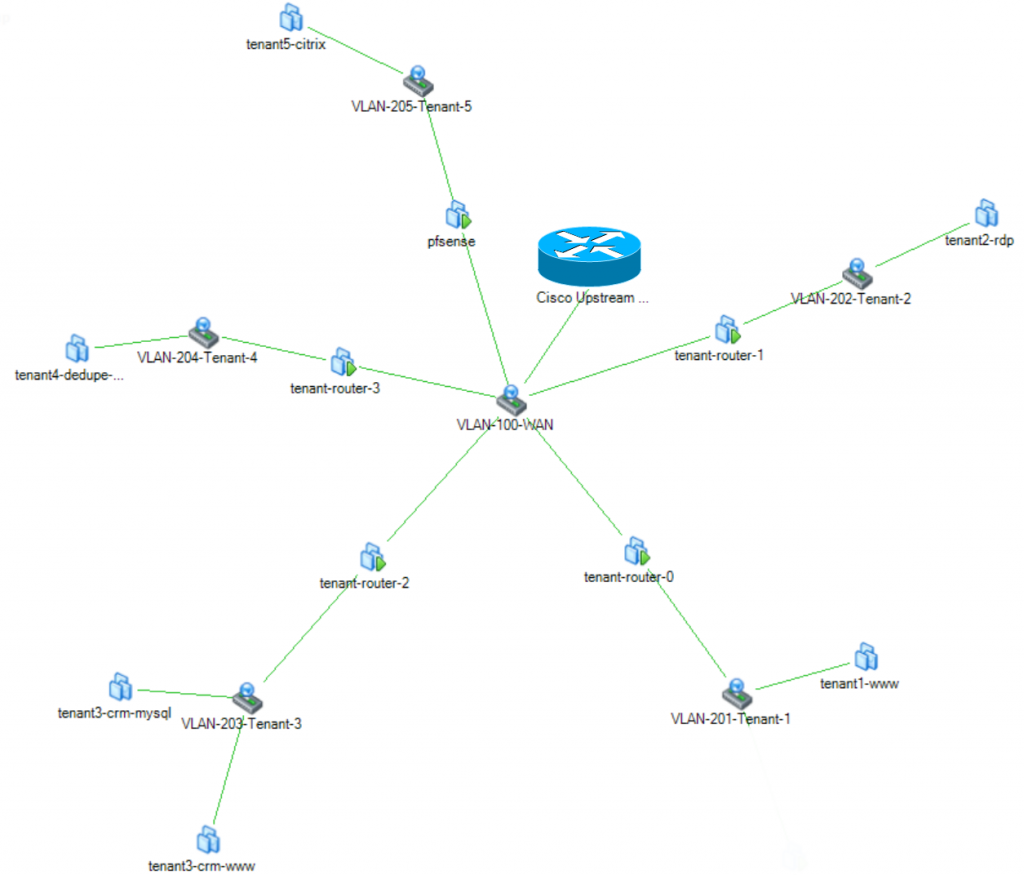
So what does it look like? Well it’s fairly boring, because essentially its just another VM that has two network cards. One NIC in the “customers” VLAN and one in the public Internet portgroup. Here in this diagram I have my VLAN 100, which has my internet IP subnet in it with no filtering. Also attached to VLAN 100 are the tenant firewalls, each has its WAN interface assigned a static public IP. Each firewall is also attached to a second VLAN that carries that tenants “LAN” traffic inside my cloud, and is where the workloads are attached.
So what’s the downside? Automation. I’m sure that I could write a script to deploy a pfSense template, assign the right IP’s and create the VLAN on my switch but that will never touch the automation of a more polished solution like NSX. But for the price, it works great!
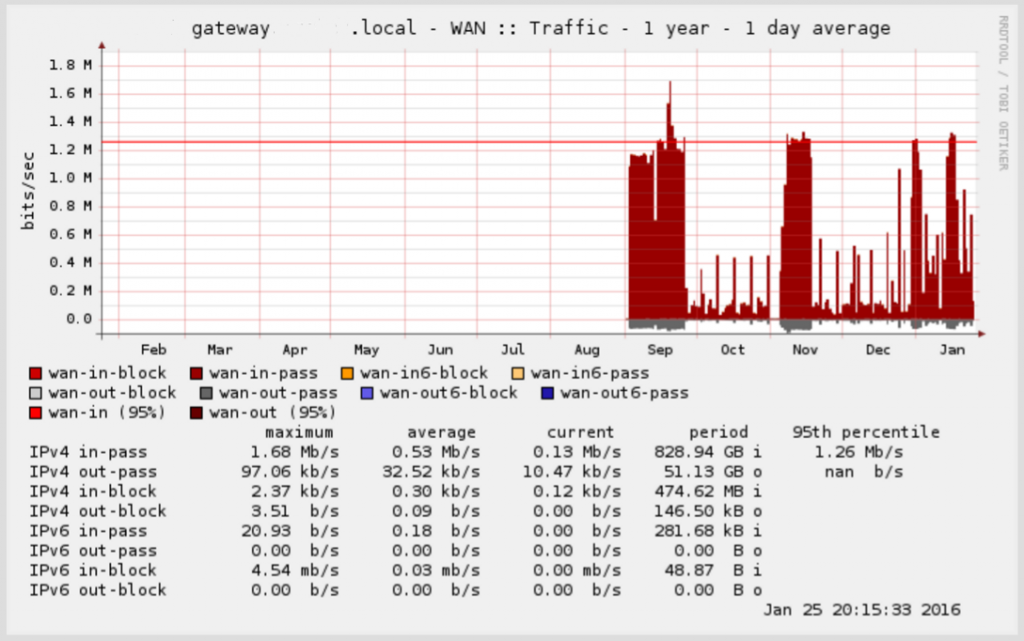
So how reliable is it? Well one of these pfSense boxes has been running since August and has only dropped VPN connectivity once for an extended period of time (a couple of hours), but as soon as I logged in and told it to connect it came right up. As far as throughput, I can easily drive 100Mbps through a VPN connection with plenty of CPU left over in the pfSense VM.
Here is a screenshot of traffic through one such firewall.
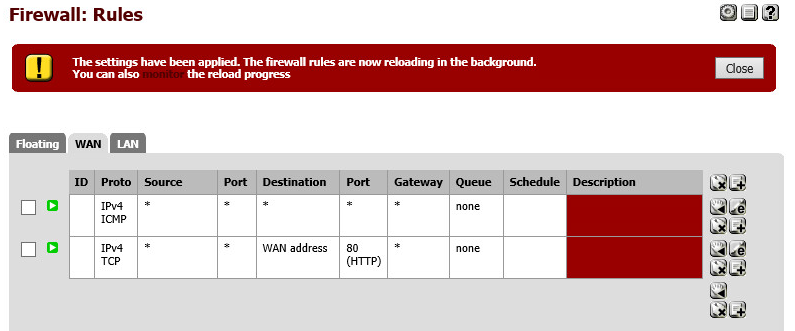
One last note. If you want to be able to administer the firewall from the WAN interface you will need to create a firewall rule to allow traffic inbound on either port 80 or 443 depending on what you are using. You may also want to allow ICMP traffic so you can ping the firewall too.
![]()