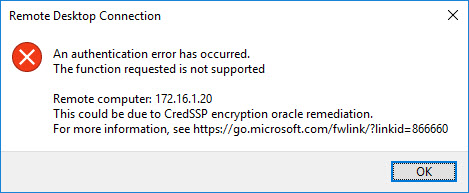
Lately, I’ve been having trouble using Remote Desktop to get into machines in my lab. The error is always the same:
What is CredSSP and why it is an issue?
(From the Microsoft KB Article)
Credential Security Support Provider protocol (CredSSP) is an authentication provider that processes authentication requests for other applications.
A remote code execution vulnerability exists in unpatched versions of CredSSP. An attacker who successfully exploits this vulnerability could relay user credentials to execute code on the target system. Any application that depends on CredSSP for authentication may be vulnerable to this type of attack.
How to fix the problem
As stated in the Microsoft KB article that I linked to in the last section, there is a fix for this issue. And if you’re
NOT like me… and keep your systems patched with Windows Updates, you have probably already patched this. But if you haven’t there are two ways to do it it.
Run Windows Updates
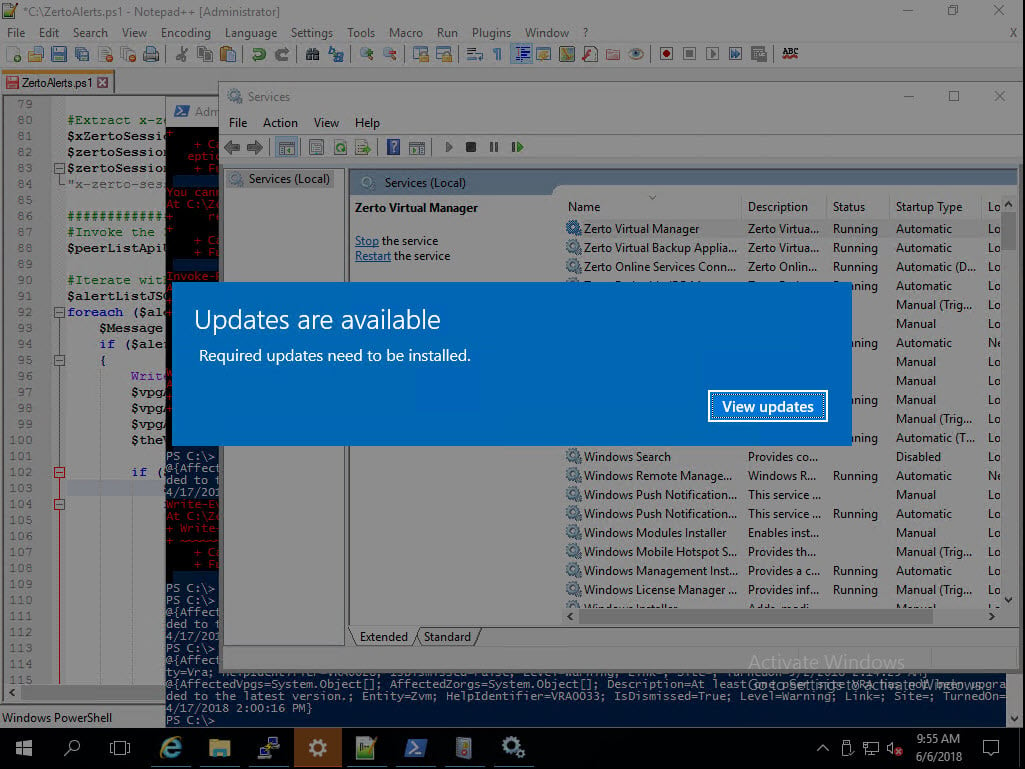
Most of my lab machines aren’t set to run updates automatically. For no other reason than just being lazy and not turning it on. So all I needed to do was log in to the console of the affected machine, where I found the “Hey stupid, install updates screen.”
Once you click view updates you will get the list of updates ready to be installed.
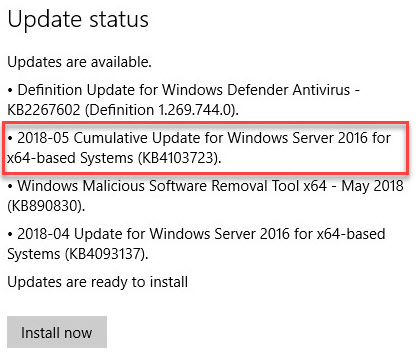
The update that I put the red box around is a cumulative update, which means that there are a bunch of updates that I haven’t installed so Windows updates is just going to apply one update that contains a bunch of fixes that I’m missing. One of which patches the CredSSP vulnerability.
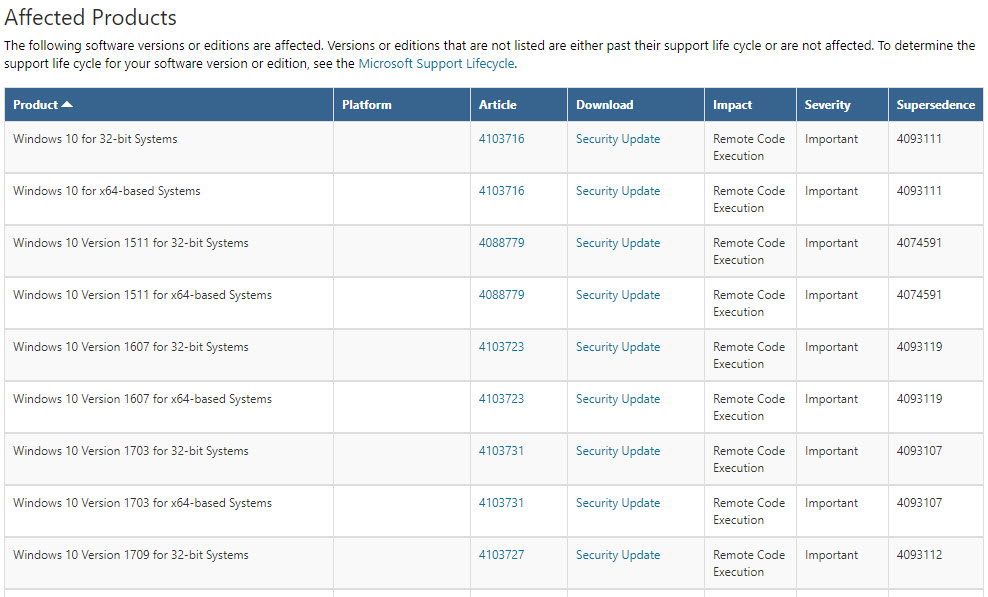
Alternative Method to patch
If for some reason you do not want to use Windows Updates to do the installation, you can be more surgical and just install the CredSSP patch. To do that navigate to https://portal.msrc.microsoft.com/en-us/security-guidance/advisory/CVE-2018-0886. Here you can download the patch specific to your system without all the other updates.
Workarounds
Although patching the vulnerability is the “right” way to fix this, it appears as though you can also change some Group Policy settings to allow unpatched clients and servers to still work together. While I wouldn’t recommend it, I do understand that sometimes a “fix” breaks something else. So if this that is your case, then check out this page where some GPO settings are discussed.
https://support.microsoft.com/en-us/help/4093492/credssp-updates-for-cve-2018-0886-march-13-2018
![]()


Has anyone received any complaints yet about RDP and WAN connections with high latency. As soon as we installed the May 2018 patches on the server the clients experienced very slow RDP connections (unworkable). We had to uninstall the patches in order to get things back to normal.
I personally haven’t, but it’s just me on my RDP machines so probably not the best comparison.
Are you talking about terminal servers? or just the admin connections are slow?